Willow Pattern
| Willow Pattern | ||
|---|---|---|
 | ||
| Game No. | 550 | |
| Voting | 6.25 points, 4 votes | |
| Developer | Greg Duddle | |
| Company | Mr. Micro Ltd | |
| Publisher | Firebird, Pubblirome/Game 2000 | |
| Musician | David Whittaker | |
| HVSC-File | /MUSICIANS/W/Whittaker_David/Willow_Pattern.sid | |
| Release | 1985 | |
| Platform | C64, ZX Spectrum, Amstrad CPC | |
| Genre | Adventure | |
| Gamemode | Single player | |
| Operation | ||
| Media | ||
| Language | ||
| Information | aka The Willow Pattern Adventure Il Pirata | |
Description[edit | edit source]

Willow Pattern is an action-adventure game that spans 64 screens. There is no scrolling; the screens are displayed using a flick-screen method. Playing as Chang, a Chinese secretary, the player fights their way through a heavily guarded garden labyrinth to free Princess Koong-Shee. Once Chang and she escape to a ship, his mission is complete.
Backstory[edit | edit source]
The game's title refers to a Chinese legend depicted in blue on white on countless tea sets: The evil Mandarin Li Chi wants to marry his daughter, Princess Koong-Shee, against her will to Duke (or, in another version of the story, to the merchant) Ta-Jin. When he learns that the princess loves the secretary Chang, the Mandarin decides to imprison her in a garden labyrinth and have her strictly guarded until her wedding to Ta-Jin. Chang then sneaks to her prison disguised as a servant, frees Koong-Shee, and escapes with her and the jewels that her father's chosen groom had brought as a wedding gift, sailing on his ship to a distant island.
Not included in the game, but only hinted at in the title image above, is the second part of the legend, in which the Mandarin discovers Chang and Koong-Shee's hiding place years later and has them killed (or, in another version of the story, has Chang killed, whereupon Koong-Shee commits suicide). The two swallows in the title image may represent the two birds into which the gods subsequently transform the lovers.
Design[edit | edit source]
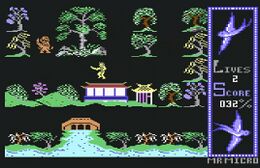
The garden labyrinth that Chang traverses in search of Princess Koong-Shee, although composed of a manageable number of repeating elements, still appears varied and is beautiful to behold in its vibrant colors — flowering trees and bushes interspersed with small teahouses, delicate fences, and picturesque waterways (left image in the gallery below).
Some parts of the maze are connected by bridges, each of which is blocked by three giants (right image). Here, Chang must cross the river by hopping from stone to stone, dodging the giants who reach for him. Since the enemies' movements are always the same, this obstacle quickly becomes tedious and, above all, annoying.
The same applies to the Far Eastern-sounding melody that accompanies the game, but it repeats every 18 seconds. Even though its tempo increases once Chang wields a sword, the music still becomes monotonous after a short time.
 |
 |
Graphics[edit | edit source]
The graphics are rendered in multicolor bitmap mode, using only a 256x192 pixel section for the garden labyrinth scenes. Since only one screen page is reserved for this in the Commodore 64's RAM (at address $6000, with the corresponding color information in the screen memory starting at address $4400), a jumble of old and new screen content is visible for about 0.2 seconds during the transition from one screen to the next.
Chang, Koong-Shee, all enemies, and all bonus items are represented by monochrome sprites of simple width and height. This makes Chang, in particular, appear very simple and occasionally somewhat ungainly. However, the author put a great deal of effort into the character animation: four sprites alternate for each of the four possible directions of movement, specifically for unarmed Chang, for "Chang with sword", and for "Chang with Koong-Shee." Only the combination "Chang with Koong-Shee and sword" does not exist; as soon as Chang picks up a weapon on his way back to the rescue ship, the princess briefly disappears.
The enemies are also animated in the same way, so that there are a total of 72 sprite definitions for the characters alone:
Hints[edit | edit source]
Controls[edit | edit source]
The player character can optionally be controlled with a joystick Control via port 2 or with the keyboard.
When using the joystick, Chang, if armed, throws his sword in the direction he was last moving by pressing the fire button. Regardless of whether he hits an enemy or not, the sword disappears afterward, leaving Chang unarmed. When crossing a river, Chang jumps as soon as the fire button is pressed.
When using the keyboard controls, the following key mappings apply:
- SPACE : Start the game.
- A / S : Left / Right.
- : / ; : Up / Down.
- SHIFT : Throw sword / Jump across river.
- H / T : Pause / Resume.
Screen Layout[edit | edit source]
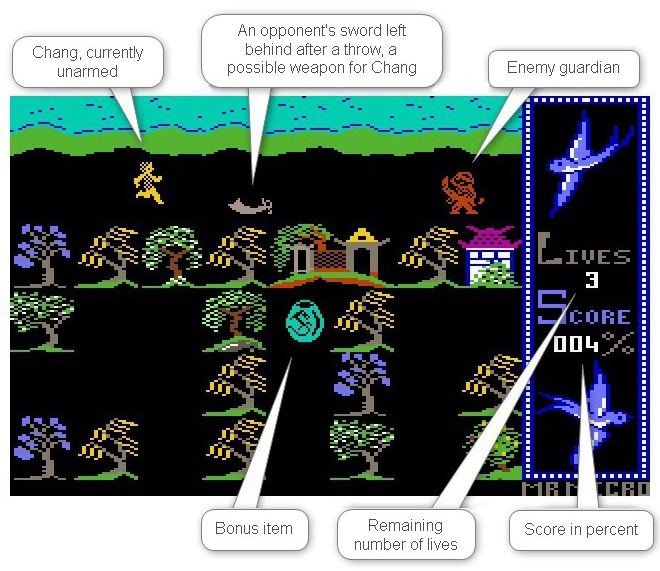
At numerous points in the garden labyrinth, passages are blocked by guardians whom Chang must defeat to continue his journey. Since he starts the game unarmed and can only use each sword for a single throw, Chang relies on collecting new weapons along the way. The easiest way to do this is by picking up swords he encounters while traversing the labyrinth (shown on the far left in the following gallery of bonus items). Chang finds a weapon in this way at a total of 14 locations in the maze. Such a find does not increase the percentage score, but successfully using the sword against an enemy increases it by 1%.
Of the remaining items, only the key to Koong Shee's prison, shown on the far right in the following illustration, is important for solving the game. The remaining bonus items increase the score — 3 apples and 2 dragon eggs by 1% each, 5 crystals and 4 gold coins by 2% each — but do not bring Chang any closer to his goal of freeing the princess and escaping with her.
 Bonus items: swords, apples, dragon eggs, crystals, gold coins, and the key to Koong Shee's prison |
Since the swords available in the maze are far from sufficient to fight his way to Koong Shee, Chang can acquire more weapons by disarming guards and taking their swords; however, this is only possible with light red and orange-colored enemies. To do this, Chang approaches a guard from the left or right until the guard throws their sword at him. If Chang then dodges back or to the side in time, without leaving the current screen, the sword falls to the ground some distance away from the enemy and can be picked up by Chang. If Chang does not take advantage of this opportunity, the opponent reclaims the sword as soon as Chang leaves the current screen; otherwise, the opponent is unarmed from that point on. Chang can choose to use a sword acquired in this way against its former owner or against another opponent (left animation in the following gallery).
Movement[edit | edit source]
Several sections of the labyrinth are only accessible via bridges (in screens B1, C4, F4, A7, and A8). As soon as Chang touches the bridge depicted at these locations, the screen changes to a scene in which Chang must cross the river by hopping from stone to stone (center image in the gallery). The bridge itself is blocked by three giants reaching for Chang. However, since this movement is perfectly regular, he only needs to ensure that he positions himself close to the next gap and jumps the moment the giant lurking in front of him clenches his fist.
If Chang changes his mind and decides not to cross the river after all, an immediate return to the shore is not possible — if he jumps back from the first stone, Chang falls into the water and loses a life. Instead, he must first cross the bridge and then return from the opposite bank.
Chang also loses a life if he falls into the water due to a misstep or being grabbed by the giants. However, he keeps any sword he may have been carrying when crossing the bridge. If, on the other hand, Chang loses a life while walking through the garden and is carrying a sword, he starts his next life unarmed.
Once Chang has freed Princess Koong-Shee, the Mandarin pursues them on their escape to the rescue ship. Against this final boss, no sword will help; only a swift escape (right image) is effective. He enters each new screen exactly 1.12 seconds after Chang and Koong-Shee, so it's impossible to shake him off. However, this movement pattern also means that a dead end poses no danger for the two: they simply need to leave the screen within 1.12 seconds and can then continue their escape in the opposite direction.
 |
 |
 |
Solution[edit | edit source]
To complete the in-game task, the player must collect the key to Koong Shee's prison, then free the princess, and finally reach the ship needed for their escape with her.
Chang has unlimited time to reach Kong Shee's prison, and only crossing rivers and disarming enemies requires quick, sometimes pixel-perfect, movements. While flawlessly jumping from stone to stone should become second nature after a short time, the movements for precisely approaching and lightning-fast dodging armed enemies, and especially judging the necessary distances, definitely require some practice.
On their way back to the ship, Chang and Koong-Shee are pursued by the Mandarin (who, in the game, looks more like the witch from "Hansel and Gretel"), in keeping with the underlying legend. This pursuer cannot be shaken off but enters every screen where Chang and Koong-Shee are located within 1.12 seconds through the same entrance they used. He then heads towards them as directly as possible. If the only way to approach them is via a detour that briefly leads away from them, the Mandarin does not recognize this possibility. However, since he can also move diagonally, while the pair can only move up/down or left/right, he has a significant speed advantage.
Map[edit | edit source]
For better orientation, the map is provided with a grid and a coordinate system, to which all subsequent location references refer.
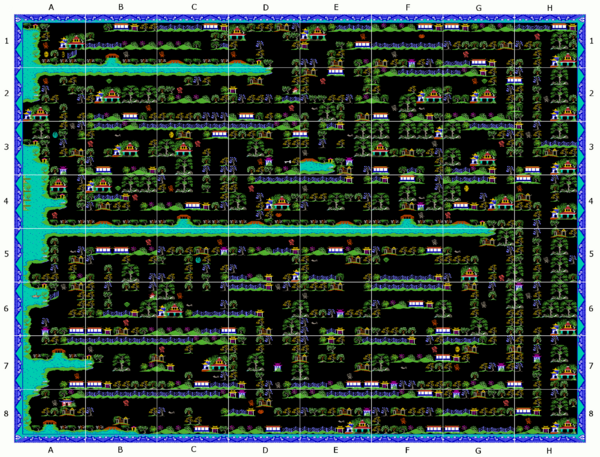
In addition to the start screen A8, the key elements for solving the game are the prison key in the screen with coordinates D3, Koong Shee's prison in A1, and the dock for the escape ship in A6. Once Chang possesses the key, the gate to the right of the princess disappears, and once he is accompanied by her, the ship becomes freely accessible.
The following map illustrates the path from the starting point to the princess (orange line, from the bottom left corner to the top left corner). This path is determined by the fact that Chang can only carry one sword at a time, necessitating the use of available swords sparingly and potentially returning later to a weapon that could not initially be acquired. For example, from starting point A1, intermediate station A6 could be reached not only via A8/A7 as shown, but also via B8/C8/D8/D7/D6/C6/B6, which would save Chang from having to cross two bridges. However, this alternative route consumes two swords, which will be needed later in the game. It is also always worthwhile to disarm enemies who are not blocking the path.
Detours that serve solely to obtain additional swords are marked in pink on this map; the short detour to the prison key is light blue. For the sake of clarity, bonus items that do not contribute to rescuing Koong Shee are not shown.
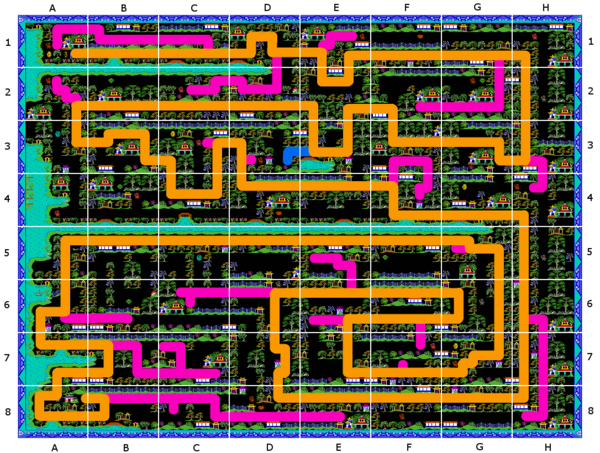
The escape to the rescue ship follows the same paths that Chang already took on his way from the starting point to the Princess's prison. The ship in Screen A6 is now freely accessible; the fence that was previously to its right has disappeared. As soon as Chang and Koong-Shee slip through the now-existing opening to the ship, the game ends with the terse message "WELL DONE":

Furthermore, the title theme, which also accompanies the start screen and the river crossings, now plays again. Legend says that Ta-Jin's ship will now take the couple to a distant island.
Cheats[edit | edit source]
In the CSDb there are several cracks with a trainer function...
 |
 |
 |
...and in the "Gamebase64" there is a version where someone has really gone wild:
 |
Alternatively, the internal data structures presented in the next section can be manipulated to create custom cheats.
Internal Data Structures[edit | edit source]
The game's internal data structures listed below allow for targeted modification of the gameplay by modifying the tables and machine instructions cited here accordingly. However, the addresses given do not refer to the loaded file, but to the game already running in main memory (i.e., after the individual program parts have been copied to their final memory location — a process that is handled differently in all copies of the game offered on the World Wide Web). Therefore, for each data structure, the address (in parentheses and in decimal format, suitable for use with POKE) where it can be found immediately after loading "Willow Pattern" in the form of CSDb-Release 102753 is also given below.
Dynamic Elements[edit | edit source]
The central control element of the game is an 8 x 8 byte table at address $42C0–$42FF. Each screen in the labyrinth is assigned a byte in this table. The higher-order nibble stores the type of opponent Chang faces in this screen, the lower-order nibble the type of bonus item:
For example, if Chang takes an opponent's sword in room X, the opponent is disarmed by clearing bit 6 of its entry in this table with the following machine language instructions (CSDb: 32347):
9E8B: LDA $42C0,X 9E8E: AND #$BF 9E90: STA $42C0,X
An opponent in room X is marked as defeated by clearing bit 7 of its entry (CSDb: 31983):
9C8F: LDA $42C0,X 9C92: AND #$7F 9C94: STA $42C0,X
| Low Nibble | Image | Type of Bonus Item | Value |
|---|---|---|---|
| $x0 | - | No bonus item | - |
| $x8 | Prison key | 5 | |
| $x9 | Dragon egg | 1 | |
| $xA | Apple | 1 | |
| $xB | Gold coin | 2 | |
| $xC | Crystal | 2 | |
| $xD | Sword | 0 |
When collecting a bonus item in room X, bit 3 of its entry is cleared (CSDb: 31319):
99C1: LDA $42C0,X 99C4: AND #$F7 99C6: STA $42C0,X
Now, if you replace the bitmask $F7 at address $99C5 in the C64's main memory — either with a debugger in an emulator or by modifying a memory dump — you can see that every entering a screen will cause the bonus item that was originally present there to reappear and be collected. The value of each item is found in a 6-byte list starting at address $4090 (CSDb: 14009), and its color in a separate 6-byte list starting at address $4080 (CSDb: 13993). When modifying the values, it is important to note that they are interpreted as packed BCD numbers ($00...$99 corresponds to a value of 0%...99%).
The following diagram shows the initial data set for the central table. As with the Maze maps, the coordinates are plotted along the edges. For example, the value $CB in the upper left corner means that an orange enemy with a sword and a gold coin await Chang in screen A1 of the Maze. As can be seen in the animation on the left at the end of the "Hints" section, this interpretation is correct.
Each time the game starts, this table is initialized by copying it from address $93C0 (CSDb: 30064).
| A | B | C | D | E | F | G | H | ||
|---|---|---|---|---|---|---|---|---|---|
| 1 | $CB | $90 | $C0 | $C0 | $C0 | $9A | $E0 | $E0 | 1 |
| 2 | $C0 | $CC | $E0 | $E0 | $ED | $9D | $CC | $90 | 2 |
| 3 | $99 | $ED | $EB | $C8 | $9D | $90 | $E0 | $90 | 3 |
| 4 | $E0 | $EC | $C0 | $EA | $90 | $9D | $EB | $C0 | 4 |
| 5 | $0D | $E0 | $C9 | $E0 | $CD | $9C | $ED | $90 | 5 |
| 6 | $90 | $EC | $CD | $90 | $9D | $C0 | $90 | $90 | 6 |
| 7 | $C0 | $90 | $ED | $90 | $90 | $ED | $CB | $00 | 7 |
| 8 | $90 | $E0 | $0D | $CA | $0D | $C0 | $E0 | $C0 | 8 |
| A | B | C | D | E | F | G | H |
The exact position of the sprites representing the objects is determined — depending on the type — from a table at address $41C0–$41FF for the guardians (CSDb: 14168–14231), from a table at $3FC0…$3FFF for the bonus items (CSDB: 13853–13906), and from a table at $8C60–$8C9F for the bridges with the giants (CSDB: 28452–28465/28467). The address ranges of two tables in the CSDb release program code are shorter than 64 bytes because the data is compressed using run-length encoding: A sequence of more than two null bytes is represented by the code `$6C` followed by the number of null bytes. Furthermore, the null bytes at the end of the bridge table were merged with subsequent zeros into a common encoding.
Static Elements[edit | edit source]
Each screen of the maze is divided into 8 columns and 6 rows, providing space for a total of 48 elements, each measuring 32 x 32 pixels. The structure of all screens is stored in a 3 KB memory area (8 x 8 spaces with 8 x 6 elements each) at addresses $8000–$8BFF, where the screens are arranged row by row, and the elements of each screen are also arranged row by row.7
The following table illustrates all the elements that make up the maze. The labels on the left and top indicate the high and low nibbles of the code that represents the respective element. For example, the first memory cell $8000 of the described memory area contains the value $2A, corresponding to the upper left corner of the light blue frame.
The codes $40–$4B are reserved for crossing the river in a separate screen and are not used in the maze.
| $x0 | $x1 | $x2 | $x3 | $x4 | $x5 | $x6 | $x7 | $x8 | $x9 | $xA | $xB | $xC | $xD | $xE | $xF | |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| $0x | ||||||||||||||||
| $1x | ||||||||||||||||
| $2x | ||||||||||||||||
| $3x | ||||||||||||||||
| $4x |
In the program code, this table can be found in a compressed form: Sequences of more than two consecutive null bytes — that is, the equivalent of a free area consisting of three or more adjacent, completely black elements — are encoded by the code $BF, followed by the number of null bytes. In this way, the memory requirement is reduced from 3 kBytes (3072 bytes) to 2586 bytes.
If you load the aforementioned CSDb-Release 102753 of "Willow Pattern", the compressed representation of the maze is located in the address range of 26297 to 28882. Anyone who would like to stroll through an empty garden where only a few lonely guards brandish their swords can, after loading this file, create space for a BASIC program by entering
POKE 144*256,0:POKE 44,144:NEW
and then type and execute the following code. The result can be seen in the left and middle images of the gallery below. And anyone who wants to plant their garden exclusively with light blue flowering trees can replace the "0" at the end of line 20 with a "1" (right image of the gallery below).
10 FOR N=26297 TO 28882:V=PEEK(N):IF V=191 THEN N=N+1:NEXT 20 IF (V<22) OR (V=27) OR (V=40) OR (V=41) OR (V=55) OR (V>58) THEN POKE N,0 30 IF (V=0) OR (V=76) OR (V=77) THEN POKE N,V 40 NEXT:SYS2087
 |
 |
 |
The following short code sequences at the start of the game are also of interest for maze modifications:
; Make ship inaccessible (CSDb: 2630) 0981: LDA #$21 ; Element "Shore with tree" 0983: STA $878B ; Save as landing point for the ship 0986: LDA #$4E ; Element "Grid" 0988: STA $878C ; Make ship inaccessible ;
; Bring Chang to the start, imprison the princess (CSDb: 30189) 9450: LDA #$38 ; Start screen number 9452: STA *$5F ; Set as current room number 9454: LDX #$4E ; Element "Grid" 9456: STX $8026 ; Restore princess's prison ; Starting coordinates of the Chang sprite at $4381/$4382 (CSDb: 14533/14534)
and the opposite direction when finding the key and freeing the princess:
; Clear the path to the ship (CSDb: 3432) 0D7E: LDA #$00 ; Element "Black Background" 0D80: STA $878B ; Overwrite/remove shore with tree 0D82: STA $878C ; Overwrite/remove gate in front of ship
; Free the princess (CSDb: 31300) 99AE: LDA #$00 ; Element "Black Background" 99B0: STA $8026 ; Overwrite/remove prison gate ;
Miscellaneous[edit | edit source]
The following table compiles a number of other interesting memory cells.
| Address | Content |
|---|---|
| $0024 | The guard in the current room is ... $00=unarmed, $80=armed |
| $0040 | Remaining number of lives |
| $005F | Number of the current screen (0="A1", ..., 63="H8") |
| $008E | Chong ist... $00=unarmed, $80=armed |
| $43CB/$43CC | Current score (packed BCD, big endian) |
The number of remaining lives is reduced in the Maze using the command 9BAF: DEC *$40 (CSDb: 31774) and when crossing a river using the command 0CC4: DEC *$40 (CSDb: 3291). If the opcode $C6 for "DEC zeropage" in these command sequences is replaced with $A5 for "LDA zeropage", the number of remaining lives is no longer decremented.
The following compilation of POKEs presents an example of a custom-built "trainer" for the game "Willow Pattern".
POKE 3291,165 :REM INFINITE LIVES AT THE BRIDGE POKE 31774,165 :REM INFINITE LIVES IN THE LABYRINTH POKE 13993+3,15: POKE 14009+3,3 :REM PLATINUM COIN WORTH 3% INSTEAD OF GOLD COIN WORTH 2% POKE 30064+7*8+0,224 :REM BRIGHT RED INSTEAD OF GRAY ENEMY IN START SCREEN "A7" POKE 31319+4,255 :REM COLLECT BONUS ITEMS MULTIPLE TIMES POKE 28452+13,0 :REM REMOVE BRIDGE IN START SCREEN
Votes[edit | edit source]
| Voting of the C64-Wiki users (10=the best vote): | ||
| 6.25 points at 4 votes (rank 792). You need to be logged in to cast a vote. | ||
| ZZAP64 | 60% (Presentation 79%, Graphics 71%, Sound 68%, Hookability 60%, Lastability 56%, Value For Money 65%) | Ausgabe 9 (Christmas & New Year 1985/1986), S. 20 |
| Spectrum Computing | 6 / 10 | March 13, 2022 - 4 votes |
| Commodore User | Graphics 5/5, Sound 3/5, Toughness 3/5, Staying Power 4/5, Value 5/5 | Ausgabe 28 (January 1986), S. 22-23 |
| Your Commodore | Originality 6/10, Playability 7/10, Graphics 9/10, Value for Money 8/10 | Ausgabe 17 (Febuary 1986), S. 49 |
| Computer Gamer | 54% (Impact 45%, Originality 55%, Gameplay 60%, X-Factor 55%) | Ausgabe 24 (March 1987), S. 54 |
| Lemon64 | 7,8 | March 13, 2022 - 41 votes |
| ASM | Grafik 7/10, Sound 6/10, Spielablauf 8/10, Motivation 9/10, Preis/Leistung 9/10 | 4/87 |
| Tilt | Intérêt 3/5, Graphisme 3/5, Bruitage 3/5 | N° 30 (Avril 1986), S. 39 |
| Universal Videogame List | 4/5 | 17. Februar 2023 |
Critics[edit | edit source]
Stephan64: "Actually, a completely stupid game... You run through a labyrinth that looks the same every time you start, along the same paths, massacre a few completely predictable enemies, get annoyed about the lack of weapons — and grab the loot lying around everywhere. Probably because of the beautiful graphics, I still find myself enjoying playing it for a while now and then. Therefore, a generous 6 points, especially for the loving design of the garden labyrinths."
Riffislam: "Willow Pattern is a game that never lets me rest. Despite the enemies being relatively simple, it's easy to lose a life. And then there's always some nasty enemy lurking right behind a doorway, leaving you with no chance. The bridge with the treacherous giants often costs me my last life. The game deserves 7 points."
Miscellaneous[edit | edit source]
Cover[edit | edit source]
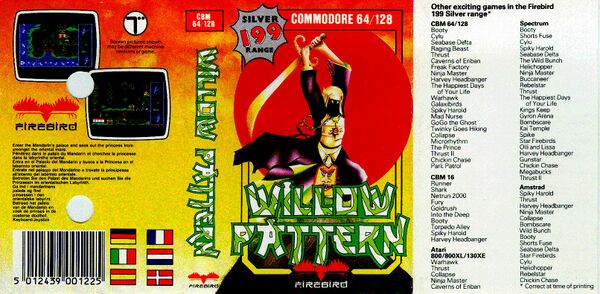
Inlay[edit | edit source]
Cassette[edit | edit source]
Theme[edit | edit source]
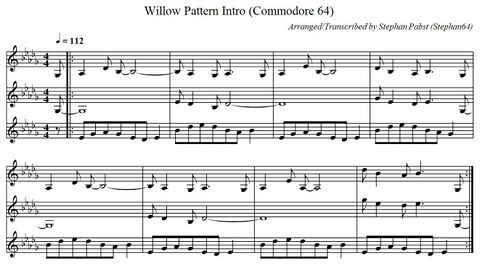
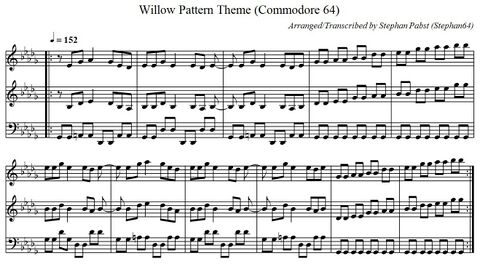
The musical accompaniment consists of two short melodies. The first melody plays while the title screen is displayed, while Chang crosses a river, and when the rescue ship is reached; the other accompanies the exploration of the garden maze. The following gallery shows these two pieces of music in standard musical notation. Once Chang is armed, the playback speed of the second melody increases to one and a half times the original speed.
For creative reuse of both pieces of music, the sheet music is also available as a PDF document (File:WillowPattern Theme PDF.pdf) and in ABC musical notation (File:WillowPattern Theme.abc.txt).
 |
 |
Fastloader[edit | edit source]
The cassette version of "Willow Pattern" uses an integrated software fast loader, which is automatically activated during loading, but only speeds up the loading process by a factor of about 1.7. A detailed analysis of the loading routines reveals the reason for this rather poor performance: Firstly, the first loaded program segment does not contain the fast loader at all, but only a short command sequence, which in turn uses the kernel to load a 1 kB module containing two independent loading routines.
On the other hand, while these loading routines use shorter encodings for 0 and 1 bits than the kernel, they are otherwise primarily optimized to obscure their own operation and prevent the game from being reconstructed by analyzing the tape data. This includes the fact that the reloaded data is encrypted by XORing with the code of the fast loader; as a result, unlike what is usually the case, more than 50% of the data consists of 1 bits, which in turn are encoded by longer pulses.
Both fast load routines read an arbitrarily long sequence of 256-byte blocks from the tape and place them — not necessarily consecutively — in the C64's main memory. What all the routines have in common is that they resynchronize the C64 with the data stream before each block, thus wasting a lot of time and space on the cassette.
The first fast-load routine expects a 7-byte header before each block. This header contains the block number (1 byte), the load address, the end address of the entire block sequence, and the entry address of the contained program segment (all addresses are 2 bytes in little-endian format; entry address $0000 means "do not jump to the program segment after loading"). This header is followed by 256 data bytes and the checksum calculated from these bytes using an XOR operation. The first fast-load routine loads three program segments into the ranges $1F00–$47FF, $0800–$1FFF, and $E000–$FFFF, and then passes control to the second routine.
This, in turn, expects a 4-byte header before each block, consisting of the synchronization identifier valid for the next block, the block number (each 1 byte), and the load address (2 bytes in little-endian format). In block number 0, 64 data bytes follow this header; otherwise, 256 data bytes follow. However, instead of terminating the data structure with the checksum, another byte follows, indicating how many additional padding bytes (between 1 and 31 bytes) follow, which are simply skipped and ignored. This extra data alone increases the data volume by a total of 1928 bytes for 120 blocks and an average of slightly more than 15 padding bytes per block. Following the checksum is an address that is accessed after the block is loaded and usually points to the fast loader itself. Many of the data elements described here are likely intended only to make it more difficult to reconstruct the program data.
The final data block contains a true masterpiece of obfuscation: it is still largely encrypted and therefore must first decode itself by byte-wise XOR operation with the second fast loader routine. It then shifts and decrypts the loaded program data by multiple XOR operations, based on four additional addresses (each 2 bytes, little-endian format) loaded from the tape. Finally, the game is started by an instruction sequence that redirects the BRK vector to the game's entry point and then overwrites itself with null bytes — the opcode of the BRK instruction.
Highscore[edit | edit source]

- Riffislam - 77% (03.04.2022)
- Stephan64 - 74% (17.03.2022)
- Ivanpaduano - 32% (17.03.2022)
- Keule - 2% (17.12.2023)
Links[edit | edit source]
- C64Games.de - Game No. 2380
- Gamebase64.com - Game No. 8609
- Lemon64 - Game No. 2856
- CSDb - Release No. 102753 (alternatively: CSDb - Release No. 19217, CSDb - Release No. 52068, CSDb - Release No. 97248, CSDb - Release No. 136945, CSDb - Release No. 153409)
- CSDb All entries
- ready64 - Game No. 507

- The SixtyFour Originals DataBase - Game No. 493
- Spectrum Computing - game no. 5688
- Willow Pattern at MobyGames
- Magazine
- ZZap64 test report
- ASM test report (pp. 16)

- Tilt test report (pp. 38)

- Commodore User test report (pp. 22)
Videos[edit | edit source]